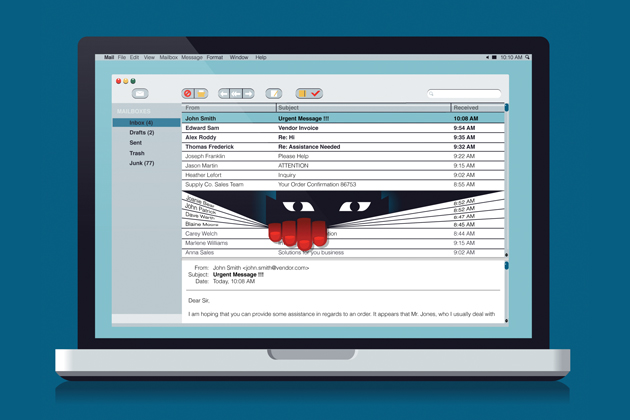
One of the fastest-growing corporate crime threats today does not exploit IT or information security weaknesses. Rather, criminals around the world are targeting the weakest link in every enterprise: humans. Learn more about the risks of social engineering fraud in "The Devil in the Details."
As criminals get increasingly sophisticated in the ways they exploit technology, it is impossible to eliminate the risk completely. It is critical for companies to establish rigorous protocols to reduce the risks of social engineering fraud, disseminate and enforce these guidelines, and regularly educate employees on new or continuing schemes as they arise. There are several easy—and often inexpensive—ways businesses can reduce the risk of social engineering fraud:
1. Require redundancies: Multiple people should have to sign off on all wire transfers, ensuring more than one set of eyes will review any potentially suspicious activity. “Dual control or the separation of duties can protect a company against fraudulent requests,” said Kristen Peed, director of corporate risk management at CBIZ. Once this policy is established, be sure it is consistently enforced and that any employees handling funds are regularly reminded of the policy and educated about common warning signs. Red flags include requests to change account numbers, expedited requests, and requests for unusual amounts, Peed added.
2. Verify via other modes of communication: Company policies should also require different forms of authentication: If a request is received by email, for example, a phone call should always be required to verify the transaction. What’s more, make sure the phone number used is one that was previously established, such as those from a corporate directory, not one listed in an email or otherwise provided by the requester. “Scammers commonly include phone numbers in an email signature and will staff that phone number in hopes that an employee will call to confirm the request by phone,” Peed said.
3. Limit all public information: In addition to any information posted to social media websites, company websites may offer thieves more intelligence than you realize. Peed urged caution with anything related to job duties or descriptions, hierarchical information and out-of-office details, as scammers often look to LinkedIn, Facebook and company websites to craft more targeted messages. Employees should also avoid posting out-of-office details. “If criminals know you are out of the country and not checking emails, they could take advantage of this and pretend they are you,” she explained.
4. Pen-test, and pen-test smarter: As part of the penetration testing process, experts can craft test phishing emails to gauge how good employees are at rooting out these schemes and how well they are following procedures. These exercises can be a particularly effective tool to boost employee education and preparation when they are reviewed in depth afterward, highlighting the methods used and their efficacy on the company’s own employees, and can be used to further tailor training to the vulnerabilities of the workforce, said Chris Blow, senior advisor at Rook Security. Some insurance policies may even cover the costs of conducting these tests as part of an effort to preventatively boost security practices, or may be able to connect customers with loss mitigation services at a reduced rate, and email phishing can often easily be incorporated into general penetration testing services. Risk managers should be asking brokers for a menu of the services offered with a cyber policy. Working through the insurance carrier to secure these services can save money not only on the testing, but potentially on future premiums as well.
5. Implement easy email tools: Simple safeguards can be integrated into company-wide email procedures to reduce the risks of phishing. Creating a centralized email address can make it easier for employees to forward suspicious messages to IT for investigation, Peed suggested. IT can then block IP addresses or domains used in the malicious messages to reduce the risk enterprise-wide. Blow recommended including an official company banner or letterhead on emails, as this provides an easy way to help employees distinguish between authentic and fraudulent messages. “It’s not going to stop anything, but the email will at least look different, and any pieces that are missing should set off an alarm for users,” he explained.
6. Review insurance options: Many companies now offer specific endorsements to crime liability insurance policies to cover losses stemming from social engineering fraud. Depending on policy language and the insurer’s interpretation, some businesses may also find a bit of relief from existing crime policies or through broad commercial liability insurance, such as all-risks policies in the London market.
