The global market for risk services is expected to approach $500 billion in 2026. The industry has never spent more capital on defense, possessed more data or deployed more sophisticated tools. Yet, in boardrooms across the globe, there is a palpable sense that the corporate defense posture is losing ground.
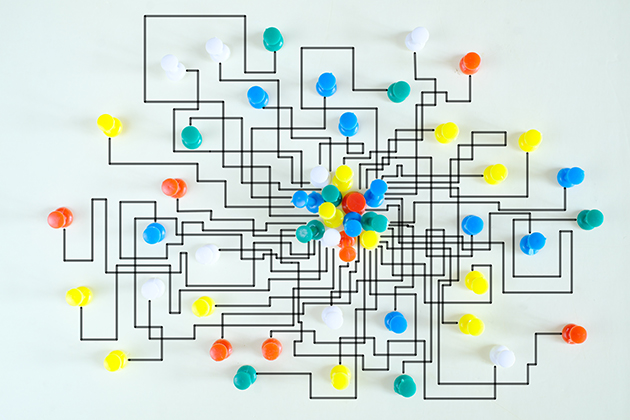
The primary threat to the modern corporation is no longer solely the state-sponsored hacker in a distant nation or the violent extremist at the gate. Instead, it comes from within: internal fragmentation that occurs when audit, cyber, physical security, HR, communications and compliance do not operate as one.
The High Cost of Fragmentation
In an era where threats move fluidly between the physical and digital worlds, corporate defense remains stubbornly analog and compartmentalized. This friction frequently results in operational failure.
In a recent case involving a major corporation, the internal audit team zeroed in on an employee for fraudulent expenses. Simultaneously, corporate security was tracking the same employee as a suspected mole providing intellectual property (IP) to a nation-state. Because audit operated in a vacuum to protect its department’s “turf,” the team confronted the employee without consulting security. The suspect immediately resigned and fled the jurisdiction, taking critical IP with them. A simple cross-functional protocol would have stopped this, but corporate turf mentalities and a lack of effective communication allowed it to happen.
A similar failure occurred at a large enterprise when a facilities department, aiming to cut guard costs, installed unvetted cameras and access controls. Treated as a budget decision rather than a security strategy, the installation inadvertently created a network backdoor. The result was a successful hack traced back to those devices. The facilities team achieved its cost-cutting objective, but in doing so, cost the company millions in remediation.
Healing the Fracture
To address these internal threats, organizations must stop confusing speed with progress. Adding more tools to a broken system only increases complexity. Instead, corporate leadership must return to anchoring security not in gadgets, but in the fundamental mission of the organization. This requires replacing fragmented objectives with a unified strategy built on four pillars:
1. Objective-Led Design
Organizations often implement a global security operations center or purchase specific platforms with an eye toward industry trends or high-profile security threats. This approach is backward. Security architecture must instead be objective-led.
The process begins by identifying the organization’s master objective and conducting a root-cause analysis to map vulnerabilities against it. If a company’s master objective is speed-to-market, security must prioritize IP protection and research integrity. If the objective is supply chain resilience, the focus shifts to logistics. When security is harmonized to the master objective, it transforms from a reactive barrier into a collaborative partner.
2. Shift from ROI to ROV
Silos persist because departments compete for budget using return-on-investment (ROI) metrics. Instead, the conversation must shift to return-on-value (ROV). When risk is viewed as anything that disrupts an organizational objective, the question changes from “What will this cost?” to “What is the value of protecting this objective?” This perspective compels departments to stop viewing themselves as separate cost centers and start viewing themselves as joint custodians of the company’s value.
3. AI as the Central Nervous System
Currently, departments rush to adopt AI in isolation—audit for fraud, safety for modeling, cyber for anomalies. Without coordination, AI acts as a force multiplier for fragmentation.
Systems must be designed so that AI acts as a central nervous system, simultaneously ingesting data from physical access logs, expense reports, network activity and more. Tools like open-source intelligence monitoring can unite these disparate elements in real time.
For example, in the insider threat case mentioned earlier, a unified AI-based platform would have correlated the expenses with the network anomalies instantly, elevating the risk to a confirmed threat before any single department acted prematurely.
4. Humans in the Loop
While technology increases the velocity of threat detection, these tools are useless without an analytical mind to digest the information and make sense of it. Organizations require trained operators who can validate AI findings, provide context and apply ethical decision-making.
This requires updated organization charts and clear ownership. When a crisis hits, teams must know exactly how to elevate concerns across department lines. If the organizational chart is a mystery, the response will be a failure.
The Return of the Risk Leader
Technology is the tool, but leadership is the true solution. The disparate nature of modern threats underscores the need for a central expert at the C-suite level who is empowered to work across departments, such as a corporate security council or a senior vice president of risk management.
Moving forward, success will not belong to organizations with the most advanced AI or the most expensive firewalls. It will belong to those that have healed the fracture lines between their departments. The threats facing modern business do not respect organizational charts; the defense can no longer afford to respect them either.
